Approov Blog
API Abuse (3)

Shielding APIs that Service Mobile Apps: Part 3 - How?
February 22, 2022
In the third part of this article series, we will look at the component parts of a shielding approach for APIs which service mobile apps and provide some guidance about what to consider when deploying a protective shield around your mobile business. Read Full Story

Shielding APIs that Service Mobile Apps: Part 2 - What?
February 15, 2022
In the second part of this article series, we are going to explore what shielding of APIs connected to mobile apps actually means. To provide some context, we will also look at how the bad guys approach attacking the APIs that connect with your mobile apps. Read Full Story

Shielding APIs that Service Mobile Apps: Part 1 - Why?
February 8, 2022
In this series of articles, we are going to explore the why, what, how and when of shielding APIs that service mobile apps. Increasingly, mobile represents a special case when it comes to security and we will make the case for some explicit steps you should take if you are working within a company that relies on mobile apps to conduct its business. Read Full Story

Hacking Financial APIs - New Report, Familiar Results
January 20, 2022
Alissa Knight’s latest security research report “Scorched Earth” was recently released. In this blog we’ll look at 3 key themes from the report and the immediate mitigations that banks, crypto companies and fintechs should implement. Read Full Story
Shift Left but Shield Right - and what are the options?
January 17, 2022
As I explained in a previous blog about the FHIR API Research Alissa Knight recently completed, “Shift Left, but Shield Right” is a strategy Alissa recommends to address the issues she uncovered in the mobile apps she tested. Read Full Story

Shift Left but Shield Right - but what does that mean?
January 12, 2022
We sponsored a major report “Playing with FHIR” by Alissa Knight, released in October 2021 (download it here) which investigated the security of mobile healthcare apps and APIs which use the FHIR standard. This report has certainly sparked a lot of debate about the security of healthcare apps and a broader discussion about who is accountable for keeping patient data safe as the ecosystem expands. Read Full Story

How to Defend against App Impersonation in 2022
November 25, 2021
Editor's note: This post was originally published in November 2021 in ThreatPost Most users who install applications through legitimate channels such as Google's Play Store or the Apple Store do so with complete trust that their information is safe from malicious attacks. This makes sense because they're the official app stores across the globe. Read Full Story
FHIR API Security Research Sparks Debate
November 9, 2021
Alissa Knight released her report “Playing with FHIR” a couple of weeks ago (download it here) about her investigations into the security of healthcare apps and APIs which use the FHIR standard. This report has certainly sparked a lot of debate about the security of healthcare apps and a broader discussion about who is accountable for keeping patient data safe as the ecosystem expands. The bottom-line is that everyone in the healthcare ecosystem needs to take steps to shield their APIs immediately. Read Full Story
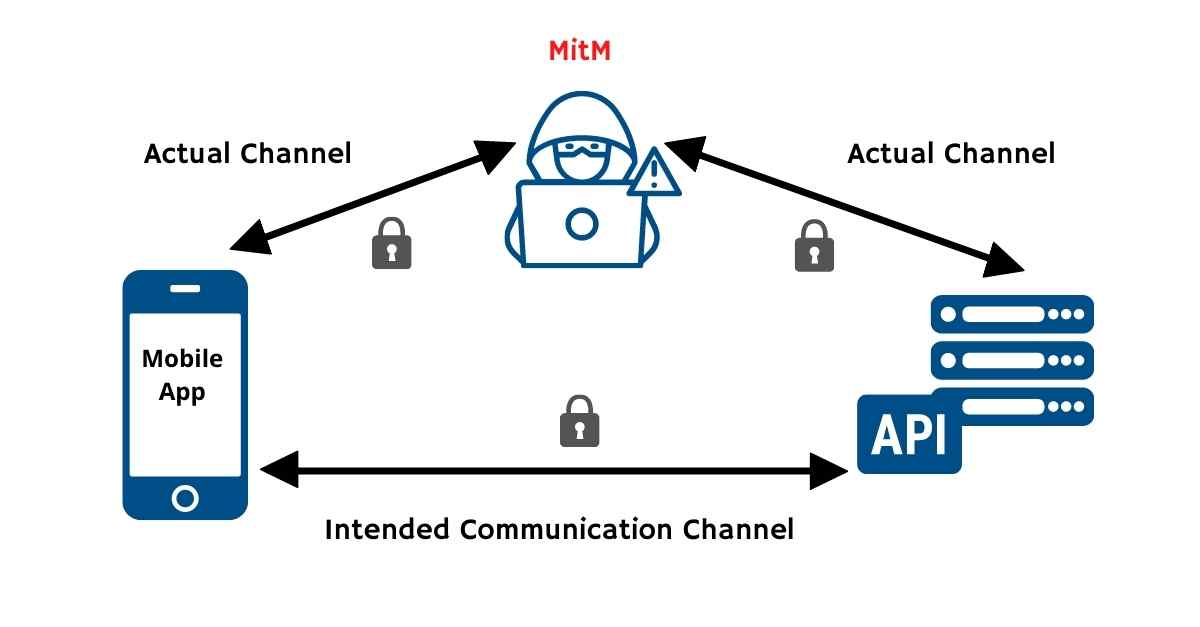
How Certificate Pinning Helps Thwart Mobile MitM Attacks
November 9, 2021
Editor's note: This post was originally published in November 2021 in Cyber Defense Magazine. The massive deployment of mobile apps is presenting new attack surfaces to bad actors and the API channel between the apps and backend services is one of the 5 defined attack surfaces in the ecosystem. In this article we will explore the challenges of defending this channel and outline some practical steps you can take to put immediate protection in place. Read Full Story

Our Certificate Pinning Configuration Tool
September 30, 2021
In this blog we introduce our new mobile certificate pinning configuration tool. This free web tool allows you to automatically generate the configuration required to pin your mobile app connections, providing an additional layer of security. Read Full Story
