David Stewart
- Advisor at Approov / Former CEO of Approov
30+ years experience in security products, embedded software tools, design services, design automation tools, chip design.

As mobile apps become increasingly paramount to operating successfully in today’s markets, a big question mark over API security is raised. Gartner has previously predicted that by 2022, “API abuses will be the most-frequent attack vector resulting in data breaches for enterprise web applications.” Since every mobile app out there is powered by APIs, securing them is clearly a top priority.
It is also a top challenge, however. Further research, again from Gartner, again from Gartner, reveals that while 70% of enterprises cite APIs as foundational to digital transformation strategies, in the face of growing attacks, API security emerges as one of the greatest issues developers and deployers must contend with.
When it comes to APIs which service mobile apps, the trouble is that anyone – including attackers – can freely install an application on a device he/she controls to reverse engineer and study it for weaknesses. This is precisely what a security researcher at AppSecure did last year with the Uber app. The researcher demonstrated that it was possible for an attacker to exploit a vulnerability that could be used to hijack user accounts via an API request and thereby track a user’s location, request rides, extract personal and payment information, and more. Uber was quick to fix the issue, but such an API vulnerability could have been used to attack potentially millions of Uber accounts.
APIs are a critical part of mobile apps and, as such, are increasingly becoming a target for hackers. Let’s consider the top five threats to APIs servicing mobile applications.
MitM attacks are often equated to eavesdropping – though in truth, the threats presented extend far beyond breaches of confidentiality. Attacks occur when mobile API traffic is intercepted by a malicious third party (the man in the middle) to covertly observe sensitive data such as personally identifiable information (PII), or extract credentials like usernames, passwords, and credit card information transmitted within API requests.
The threats don’t end there, however. The attacker can also alter the content of API communications between the app and the server by changing request parameters or results returned by the server. For example, an attacker could take control of a billing API to redirect payments made by the user to his/her own account.
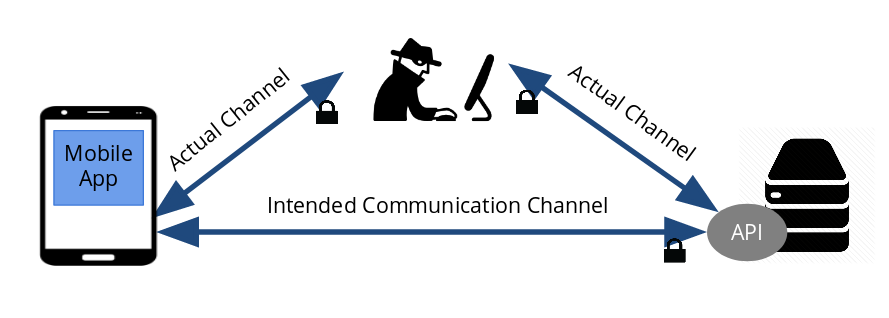
(Image source: approov.io)
It’s not just active, human agents that are looking to harvest sensitive or business-critical data exposed though mobile APIs – automated bots and data scraping systems are after it as well. Web application firewalls (WAFs) and API gateways are generally insufficient protections against API scraping bots, which mimic genuine app traffic and use correct API protocols, keys, and authentication. This means that API requests of this type look exactly the same as genuine requests, and so are extremely difficult for traditional perimeter defences to detect and even harder to block.
Automated scraping systems are capable of executing various high-impact attacks. These range from nefarious competitors looking to scrape data pertaining to pricing information (so they can undercut and thereby steal customers and revenue) to the wholesale harvesting of PII to sell on the dark web – which of course can lead to significant fines in our highly-regulated business world. Other threats include the large-scale creation of fake accounts to support fraudulent activities such as phishing, increased costs from cloud providers as you process fake traffic, and potential brand and reputation damage.
New research from security and content delivery company Akamai reveals that APIs are becoming a major target for credential stuffing attacks. Such attacks occur when login credentials (username/password combinations) obtained from a data breach against one company are used by malicious actors to attempt to login to another service or mobile application. Cybercriminals can steal the credentials themselves, or, as is more often the case, purchase huge lists – often containing millions of username/password combinations – from black markets on the dark web. Combined with purpose-built tools that use bots to perform millions of malicious login attempts at once – with the hope that a certain percentage of them will work – credential stuffing is a growing threat to businesses worldwide.
While, traditionally, credential stuffing attacks have primarily targeted user-facing login pages on the web, Akamai’s research shows a growing trend in attackers targeting APIs – particularly in the financial services industry. According to the report, between December 2017 and November 2019, of the 85.4 billion credential stuffing attacks tracked by the study, nearly 20% (16.5 billion) were against hostnames that were clearly identified as API endpoints. In the financial services industry, the trend was even more pronounced – 473.5 million API attacks against financial organisations were recorded during the period, at times accounting for 75% of login attacks.
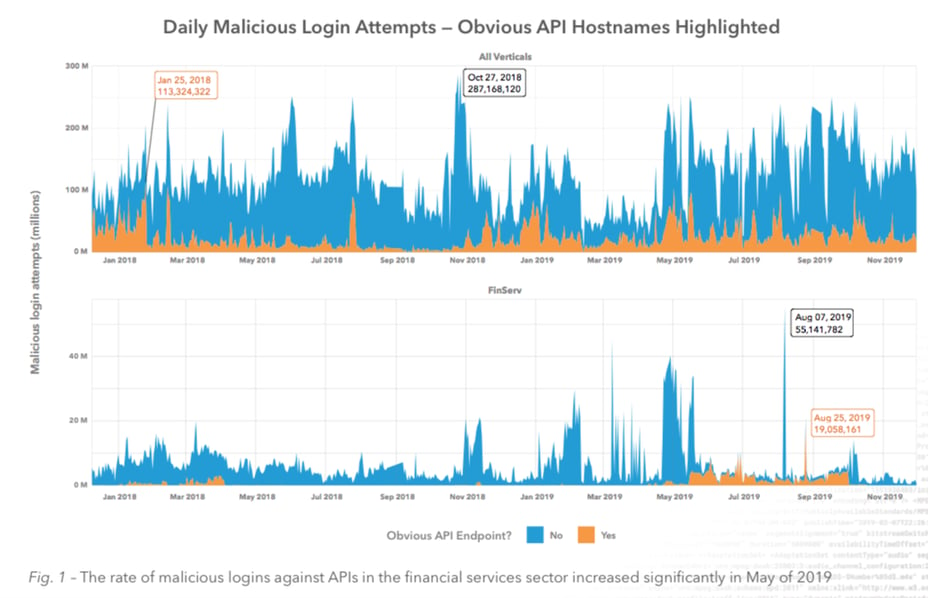
(Top graph shows all industry verticals, while the bottom graph is focused solely on financial services. Source: akamai.com)
App impersonation, as its name implies, involves cybercriminals creating a copycat, malware-infested version of your app and tricking your would-be customers into downloading it. The cybercriminal creates a cloned version that looks, behaves, and has the same functionality as the original app, though also performs malicious activities. Some fake apps are designed to harvest user credentials or other sensitive data, others to aggressively display advertisements to generate ad revenue, and still more to commit fraud. Another threat involves an attacker reverse engineering your API protocol and building new software that impersonates the real app to make arbitrary API calls, or otherwise access your backend infrastructure to communicate with and scrape information from your servers.
Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks occur when a large number of requests are sent to the API at once. The goal of the attack is to bring the targeted application down, or at least make it unusable. During an attack, genuine customer requests are slowed down or lost and the application may become defunct – impacting user experience, damaging your reputation, and potentially costing you customers and revenue. While rate limiting strategies – used to control the number of API calls an app or user can make within a given time frame – are often deployed to mitigate the impact of DoS attacks, an attacker can defeat them relatively easily by keeping request frequencies below the trigger limit.
Businesses leave themselves exposed to huge financial and reputational risks if they leave their APIs open to abuse. Standard methods to protect APIs such as API keys, user authentication tokens, and transport layer security (TLS) encrypted channels are no longer enough to deal with the growing threat landscape. While popular, API keys represent a particularly weak line of defence as they must be published in – and are relatively easy to extract from – the mobile app. Hackers can easily reverse engineer an app to extract the API key using a tool like Mobile Security Framework, or launch an MiTM attack to steal the key for later reuse in replay attacks by automated scripts for data scraping or fake account creation.
It is vital that organisations are aware of the weaknesses in their API access procedures and not just the vulnerabilities in the APIs themselves to ensure that they are protected against the threats that have been outlined in this article. All is not lost, however. Effective API security can be achieved through the golden triad of “verified user, verified channel, and verified app.” To find out more, download our Mobile API Security E-Book and take a look at this series of articles to understand the security techniques that can be deployed to protect a mobile API.