An OWASP AppSec California 2018 Talk

The fifth annual OWASP AppSec California was held in late January 2018 on the beach in Santa Monica. AppSec California is organized and run by an all-volunteer staff, and they put on a great conference — highly recommended. Besides excellent content and a chance to interact with many interesting colleagues, who wouldn’t want to hang out on the beach for a few days?
An overview of the event can be found on the AppSec California 2018 website, including links to many of the slides used during the presentations. Most presentations were video taped and are available on you tube.
My talk on API Underprotection was given to a standing room only crowd which asked some very good questions at the end.
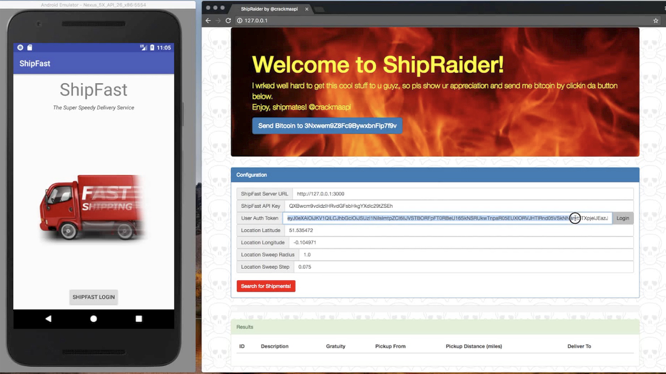
In the video, you’ll understand API security by following the evolution of the ShipFast courier service API, its branded backend service and mobile Android client, and its attacker, ShipRaider, used by both malicious and legitimate couriers to exploit the API for their own ill-gotten gains.
API User and Abuser
We start with static API keys and OAuth2 user authorization, discussing API security threats and how to counter them. Along the way, TLS, certificate pinning, HMAC call signing, app hardening, white box crypto, and app attestation are considered to strengthen your API security posture, but ShipRaider will be working hard trying man in the middle attacks, app decompilation and debugging, exploit frameworks, and other reverse engineering techniques to keep stalking you.
It’s a fast-moving overview of the cat and mouse API protection problem on mobile and provides a sense of emerging tools and techniques which enable a significant step change in API security as well as illustrating why user authentication is not enough.
ShipFast and ShipRaider are open-sourced by CriticalBlue and are available on github with stories of some additional attack-defense scenarios. You’ll walk away with access to a fully worked open source example and some additional homework assignments if you want to go deeper. A more thorough overview of mobile API protection may also be of interest.
